XChat Claims Encryption but Keys Sit on X's Servers
XChat launched April 24 promising end-to-end encryption, but security researchers found private keys stored on X's own servers, no certificate pinning, and a four-digit PIN as the only defense.

When XChat landed on the iOS App Store on April 24, the mood at X was celebratory. Lead designer Benji Taylor called it "just the beginning of what we're building for messaging." The official line was simple: "Chat with anyone on X. Completely private."
Within hours, iOS security research group Mysk had intercepted XChat's network traffic. What they found undermined every privacy claim X had made.
TL;DR
- XChat's encryption keys are stored on X's own servers, not on your device
- A four-digit PIN is the only thing protecting them from X staff or attackers
- Missing certificate pinning let Mysk decrypt network traffic during testing
- Photos transmit with GPS metadata intact, despite the "no tracking" marketing
- EFF advises against XChat for anything sensitive until an independent audit happens
The Promise
X positioned XChat as a competitor to Signal: end-to-end encrypted, PIN-protected, with no ads and no tracking. The App Store listing promised disappearing messages, screenshot blocking, and encrypted audio and video calls. "Bitcoin-style encryption" was the shorthand used in promotional materials.
The app does use the Juicebox protocol, a key-management framework designed to distribute encryption keys across multiple "realms" so no single party can reconstruct them. On paper, that's a reasonable architecture for protecting private communications.
In practice, all of XChat's realms are hosted at x.com.
What Researchers Found
The Juicebox Problem - Security researcher Tommy Mysk documented the core flaw within hours of launch. While Juicebox splits keys across multiple custodians so that no single entity holds the complete set, all of XChat's key storage endpoints resolve to the x.com domain. X controls every realm. The distribution that Juicebox aims to provide doesn't exist here. Mysk's conclusion: "X could theoretically reconstruct users' private keys and access their messages, contradicting the core promise of end-to-end encryption."
The PIN Door - The four-digit PIN is the only layer standing between an attacker and those server-stored keys. Cryptographer Dr. Matthew Garrett had warned about this design before launch. A four-digit PIN has 10,000 possible combinations. Against an adversary with access to X's servers, a brute-force attack isn't theoretical.
Cleartext Traffic - XChat doesn't implement certificate pinning. When Mysk ran the app through a proxy during testing, they intercepted and decrypted its network traffic without resistance. Certificate pinning is a standard defense that tells an app to reject connections that don't present a specific trusted certificate. Without it, network traffic analysis becomes straightforward. What Mysk observed during their interception session showed key management requests flowing to x.com domains:
[Proxy interception - XChat session, April 24 2026]
Host: api.x.com
X-Juicebox-Realm: xchat-realm-1.x.com
X-Juicebox-Realm: xchat-realm-2.x.com
X-Juicebox-Realm: xchat-realm-3.x.com
All realms resolve to X-controlled infrastructure.
Key reconstruction: possible by X.
No Forward Secrecy - Proper end-to-end encryption generates new session keys for each conversation, so a key compromise doesn't expose older messages. XChat doesn't do this. Security researcher Varun Badhwar put it plainly: "It means the end-to-end encryption claim depends on X's policies, not on math."
The Metadata Trail - X's App Store privacy label discloses collection of contact information, identifiers, usage data, and diagnostics, all linked to user identity. This is the label X itself submitted to Apple. The "no tracking" marketing doesn't align with it. Photos shared through XChat are transmitted without stripping GPS coordinates or camera details. As analyst Luke Dixon noted: "Metadata reveals who you are communicating with, when, and for how long." There are also unconfirmed reports that usage data feeds into Grok training pipelines - X hasn't addressed this publicly.
How It Compares to Signal
| Feature | XChat | Signal |
|---|---|---|
| Key storage | X's servers | On your device |
| Open source | No | Yes |
| Independent security audit | None | Multiple |
| Forward secrecy | No | Yes |
| Certificate pinning | No | Yes |
| Metadata collection | Yes (per privacy label) | Minimal |
| PIN mechanism | Server-side, 4-digit | Device-side, optional |
Badhwar set out the three tests a genuine privacy app should pass: device-only key storage, open-source code, and independent audits. His verdict on XChat: "It doesn't clear any of those three bars."
Cooper Quintin, a senior staff technologist at the Electronic Frontier Foundation, was more direct: "Given XChat's history of security vulnerabilities, I would hesitate to use this until it's received a thorough outside auditing."
 XChat's iOS interface highlights privacy, but security researchers dispute whether the underlying architecture delivers it.
Source: 9to5mac.com
XChat's iOS interface highlights privacy, but security researchers dispute whether the underlying architecture delivers it.
Source: 9to5mac.com
X hasn't published any response to Mysk's findings. The company's help pages do acknowledge, in fine print, that the key architecture "could allow a malicious insider or X itself" to access conversations under certain conditions - a disclosure that sits in stark contrast to the "completely private" marketing.
This Isn't Surprising Given xAI's Track Record
XChat's security problems don't appear in a vacuum. The xAI rebuild following its cofounder departures raised questions about whether the company had retained enough security expertise to build a messaging app correctly. The Juicebox-based architecture looks like an attempt to adopt a credible privacy framework without accepting its constraints - all the naming, none of the independence.
There's also a corporate incentive structure that cuts against genuine privacy. X needs your conversation data. Grok, the AI assistant integrated into X's platform, improves through training data. A messaging app that encrypts conversations from X's own engineers would work against that interest. The architecture Mysk described is consistent with a system designed to maintain plausible deniability about access rather than to prevent it.
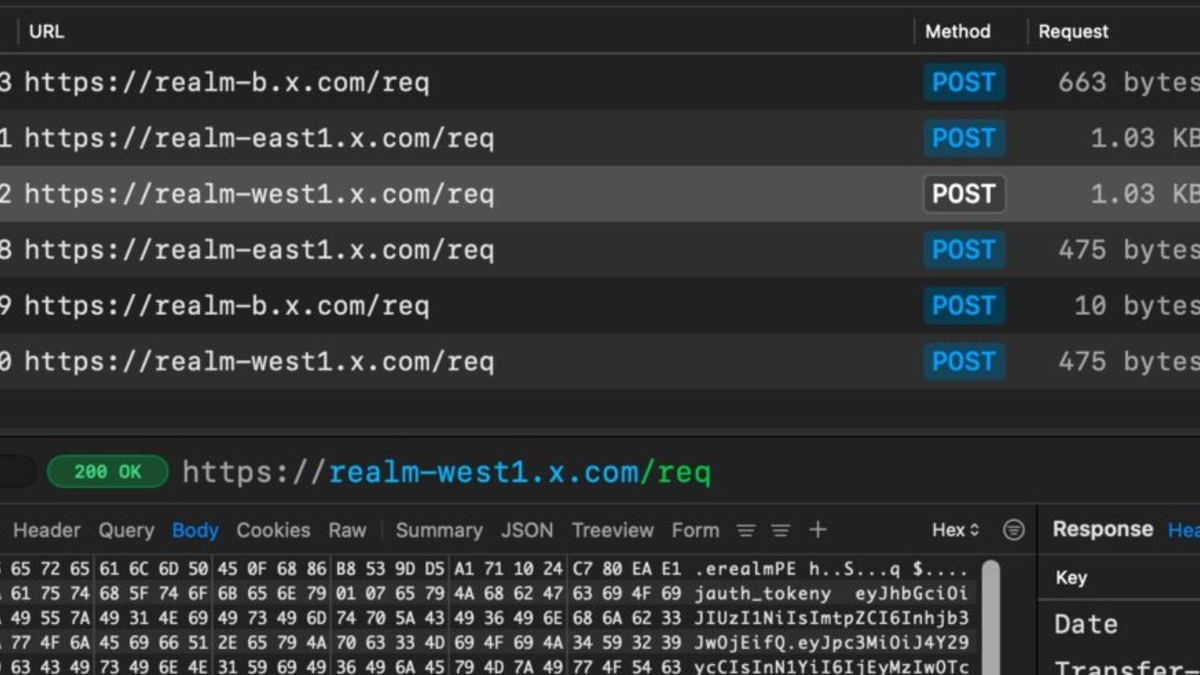 Mysk's analysis showed all Juicebox realms resolving to X-controlled infrastructure, negating the protocol's key distribution guarantees.
Source: cyberinsider.com
Mysk's analysis showed all Juicebox realms resolving to X-controlled infrastructure, negating the protocol's key distribution guarantees.
Source: cyberinsider.com
What To Do Now
XChat is live, free to download, and already being promoted across X's platform to hundreds of millions of users. If you're deciding whether to install it:
- Don't use XChat for sensitive conversations. The architecture gives X access under conditions the company itself acknowledges. The encryption marketing doesn't reflect the actual security model.
- Use Signal for anything private. Keys stay on your device, the code is open source, and multiple independent audits have verified the implementation.
- Revoke XChat's contact access in iOS Settings > Privacy & Security if you've already installed it. The app links contact information to your identity.
- Strip GPS metadata from photos before sharing them through XChat if you choose to use the app. Every image carries coordinates unless you remove them manually.
- Wait for an independent security audit. If X commissions and publishes a genuine third-party review of XChat's key management architecture, the picture could change. Until that happens, the EFF's guidance is the right default.
The app replaces X's Communities feature, which is being shut down. It's a real product, not vaporware. X will push it hard. That makes the security gap between the marketing and the implementation a problem for a very large number of people.
Sources:
- Mysk: XChat Encryption Claims - Implicator
- XChat iOS launch with security concerns remaining - CyberInsider
- X launches stand-alone XChat app on iOS - TechCrunch
- XChat launches with encryption and privacy concerns - BigGo Finance
- XChat standalone iOS app - CyberInsider
- XChat, X's standalone messaging app - 9to5Mac
- X launches standalone XChat messaging app on iOS - The Tech Portal
- Elon Musk's XChat is more like Facebook Messenger than Signal - Symplexia
Last updated
