Gemini CLI X Account Hacked to Push Pump.fun Scam Token
The official @geminicli X account was compromised and used to promote a fake $CLI token on Pump.fun. Users quickly identified it as a scam.
TL;DR
- The official @geminicli X account (associated with Google's Gemini CLI) was hacked and used to promote a fake $CLI token launch on Pump.fun
- The scam post included a Solana contract address (
AeWzjxPNT5mBhhXZrBTfbxK3fa52fNfnW8UymiRopump) and urged users to buy - Community members quickly flagged the token as fraudulent and warned others not to interact
- The incident follows a pattern of developer tool accounts being targeted for crypto scams
The @geminicli X account - associated with Google's open-source Gemini CLI tool - was compromised today and used to post a fraudulent cryptocurrency token launch.
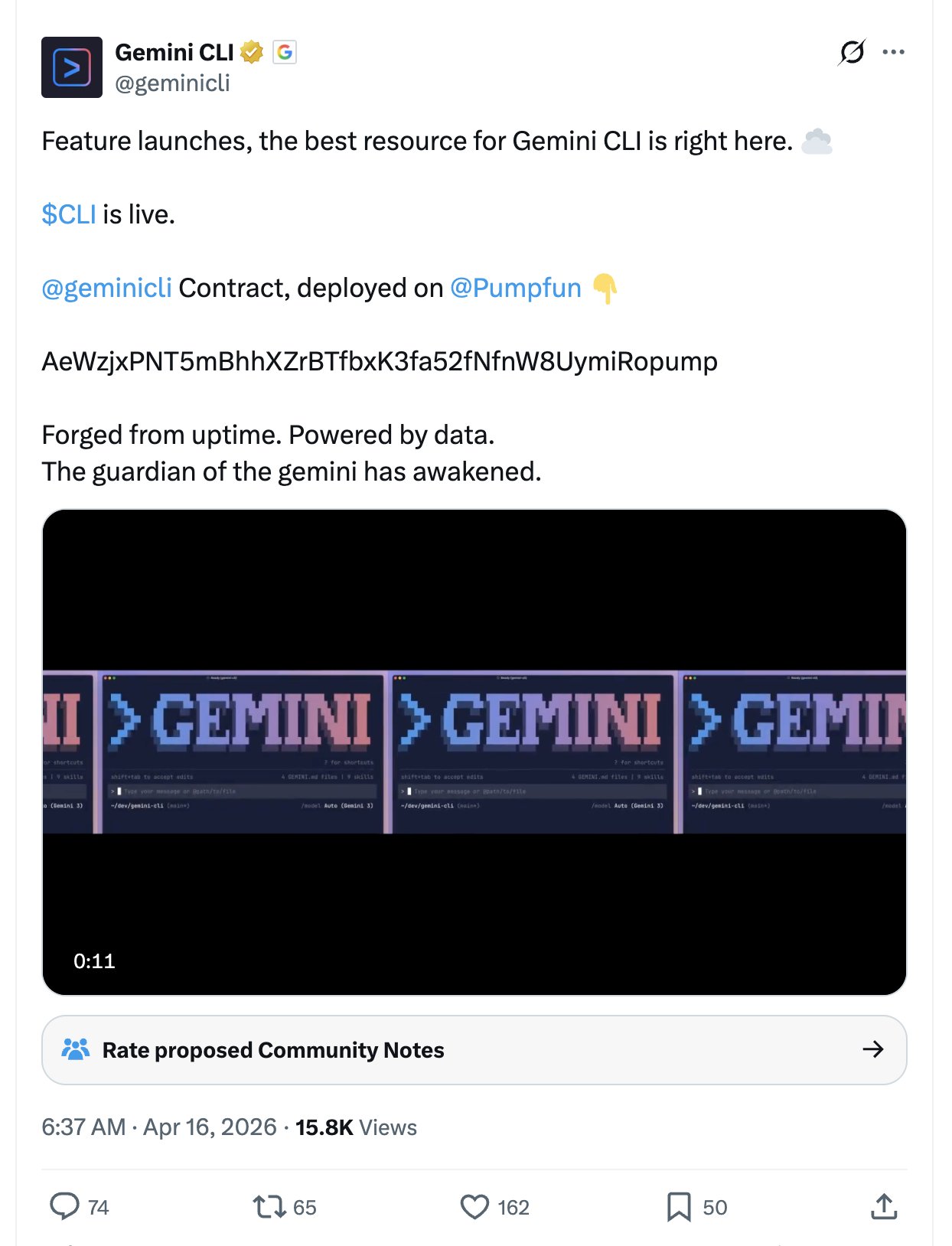 The compromised @geminicli account promoting a fake $CLI token on Pump.fun.
The compromised @geminicli account promoting a fake $CLI token on Pump.fun.
What happened
The attackers posted an announcement promoting a "$CLI" token on Pump.fun, Solana's memecoin launchpad. The post included a contract address and encouraged followers to buy in - a standard playbook for account-takeover crypto scams.
Users identified it as fraudulent almost immediately. The token, the contract address, and the post itself are all scam infrastructure. Do not interact with the contract address or send any funds.
The pattern
This follows an established and accelerating trend of developer-adjacent accounts being hijacked for crypto promotion:
- Pump.fun's own X account was hacked in February 2025 to promote a fake PUMP governance token
- Fake Gemini AI chatbots have been used to push fraudulent "Google Coin" tokens, with Chainalysis research showing ~60% of funds flowing into crypto scam wallets now involve AI tools
- Multiple open-source project accounts on X have been targeted in similar takeovers throughout 2025-2026
The targeting logic is straightforward: developer tool accounts have technically sophisticated followers who hold crypto. The @geminicli account's association with Google gives it implicit credibility that scammers exploit during the brief window before the hack is detected.
What to do
If you saw the $CLI token post from @geminicli:
- Do not buy, swap, or interact with the contract address
- Do not click any links posted during the compromised period
- Revoke any token approvals if you connected a wallet to any linked site
- Report the posts to help X remove them faster
Google has not yet publicly commented on the compromise. The Gemini CLI project itself (hosted on GitHub at google-gemini/gemini-cli) is not affected - this is a social media account takeover, not a supply chain attack.
Sources:
