Cisco Buys Astrix for $400M to Lock Down AI Agent Keys
Cisco closes its $400M acquisition of Astrix Security, folding a non-human identity platform into Cisco Identity Intelligence to govern the API keys and OAuth tokens powering enterprise AI agents.

Every AI agent your company deploys needs credentials. An API key for the LLM. An OAuth token to read Slack channels. A service account to write to the production database. Nobody tracks them. Most never get rotated. And until now, no major security platform was built to care about any of that.
Cisco's $400M acquisition of Astrix Security, announced this week, is a direct response to that gap. Astrix has built a platform specifically for governing non-human identities (NHIs) - the API keys, OAuth tokens, and service accounts that AI agents carry when they act inside enterprise systems.
TL;DR
- Cisco paid ~$400M for Astrix Security, founded in 2021 by two Unit 8200 veterans
- Astrix governs non-human identities: API keys, OAuth tokens, service accounts, and AI agent credentials
- Only 24% of organizations currently monitor what their deployed agents are doing (Cisco AI Readiness Index)
- Integration targets: Cisco Identity Intelligence, Duo IAM, Cisco Secure Access, and Splunk
- Zero customer churn in 15 months; customers include NetApp, Xerox, Priceline, and Workday
The Problem Astrix Is Built to Solve
When a developer connects an AI agent to Salesforce, it normally receives an OAuth token scoped to their personal account permissions. That agent then runs unattended, taking actions across the CRM for months. If the developer leaves, the token stays live. If the agent gets compromised, the attacker inherits full CRM access - and nobody gets an alert.
The Credential Sprawl Nobody Planned For
A single AI-powered workflow can touch a dozen services. Here's what that looks like in practice for a typical enterprise deployment:
# Example: untracked AI agent credentials in a sales automation workflow
agent_id: "sales-outreach-bot-v3"
openai_api_key: "sk-proj-..." # global org key, no rate limit
salesforce_oauth: "..." # full admin-scoped, no expiry
slack_bot_token: "xoxb-..." # all workspace channels
notion_secret: "secret_..." # all databases, read+write
hubspot_api_key: "..." # marketing, legal, finance data
created_by: "[email protected]"
last_rotated: "2024-11-03" # 18 months ago
scope: "not documented"
This isn't hypothetical. It's the default state for most enterprise agent deployments today.
Agents Aren't Like Applications
Traditional service accounts at least have a defined scope and a human who owns them. AI agents are different - they reason about what they need, request access dynamically, and act autonomously in ways their creators didn't anticipate. Alon Jackson, Astrix's CEO, put it directly in a recent interview: "AI agents can be manipulated, abused, or behave unpredictably - just like a human employee going rogue."
The difference is that a human employee can't simultaneously process a mortgage refinancing for a customer and modify your Slack workspace configuration. An agent with the wrong token set can.
Jackson argues the scale of the problem dwarfs anything the industry has seen with human identity: "AI-driven identities will be 100x more significant and complex than traditional user security." Gartner ranked NHI security above AI itself in their 2025 cybersecurity trend list - validation that Astrix was building in the right direction.
This kind of attack surface showed up in practice earlier this year when the LiteLLM SQL injection vulnerability was exploited within 36 hours of disclosure, exposing just how quickly a compromised API gateway can cascade into broader infrastructure damage.
What the Platform Does
Astrix's core product covers four areas. Each targets a different phase in the credential lifecycle.
Discovery and Governance
The platform maps every non-human identity connected to your systems - API keys, OAuth credentials, service accounts, and AI agent tokens. Discovery runs continuously across AWS, GCP, Azure, and major SaaS platforms including Slack, Jira, Salesforce, and Microsoft 365. The output is a live inventory of what's connected, what permissions it carries, and whether those permissions are still appropriate.
Access Lifecycle Management
Agents get provisioned with minimum required privilege, reviewed on a configurable schedule, and decommissioned when their task is done. Astrix handles the full lifecycle rather than just the initial provisioning step - which is where most identity tools stop.
Threat Detection and Response
The platform monitors for anomalous agent behavior and compromised credentials in real time. Cisco's integration roadmap routes this telemetry into Splunk for SOC teams, giving analysts the same tooling they already use for human identity incidents.
Secrets Management
Credentials are stored in a centralized vault across all connected cloud and SaaS systems. Rotation is automated. The goal is eliminating the last_rotated: 2024-11-03 problem from the config block above.
 Cisco previewed its agentic security platform at RSA Conference 2026 in March, before finalizing the Astrix acquisition.
Source: newsroom.cisco.com
Cisco previewed its agentic security platform at RSA Conference 2026 in March, before finalizing the Astrix acquisition.
Source: newsroom.cisco.com
How It Plugs Into Cisco
Cisco isn't buying Astrix to sell it as a standalone product. The integration plan is layered across three existing platforms.
Cisco Identity Intelligence
Astrix slots directly into Cisco Identity Intelligence, extending the platform's scope from human identities to non-human ones. The combined system can discover, authenticate, and authorize both types of identity under a single policy engine. For security teams, this means agent access shows up in the same dashboard as user access - rather than in a separate tool that nobody watches.
Duo and Secure Access
Cisco extends zero-trust access controls - currently built for human users through Duo - to AI agents. In practice, an agent trying to access a system routes through the same policy enforcement point as a person would, with the same network-level visibility and the same ability to block based on anomalous behavior.
Cisco had already been building in this direction. The DefenseClaw open-source framework, released at RSA 2026, handles skill scanning and MCP server security before an agent runs. Astrix fills the identity and credential layer that DefenseClaw doesn't cover.
Compatibility at a Glance
| Layer | Coverage |
|---|---|
| Cloud platforms | AWS, GCP, Azure |
| SaaS | Slack, Jira, Salesforce, Microsoft 365 |
| Cisco platforms | Identity Intelligence, Secure Access, Duo IAM |
| SIEM | Splunk (via telemetry integration) |
| Deployment | SaaS, no agents required on managed systems |
The Numbers Behind the $400M
Cisco paid around $400M for a company that had raised $85M in total - a Series A led by CRV and Bessemer Venture Partners, then a $45M Series B led by Menlo Ventures' Anthology Fund (which invests in partnership with Anthropic).
The multiple is steep until you see the retention metrics. Astrix reported zero customer churn in the 15 months leading up to the acquisition, with a Net Promoter Score of 9.4. Those numbers are unusually strong for a security product, where switching costs aren't always high enough to keep customers loyal if the product disappoints.
Named customers include NetApp, Xerox, Priceline, and Workday - enterprise accounts with real NHI complexity and real security budgets.
The market backdrop is also in Cisco's favor. Peter Bailey, SVP of Cisco's Security business, cited the company's AI Readiness Index finding that only 24% of organizations can effectively monitor agent activity. That 76% gap is the addressable market.
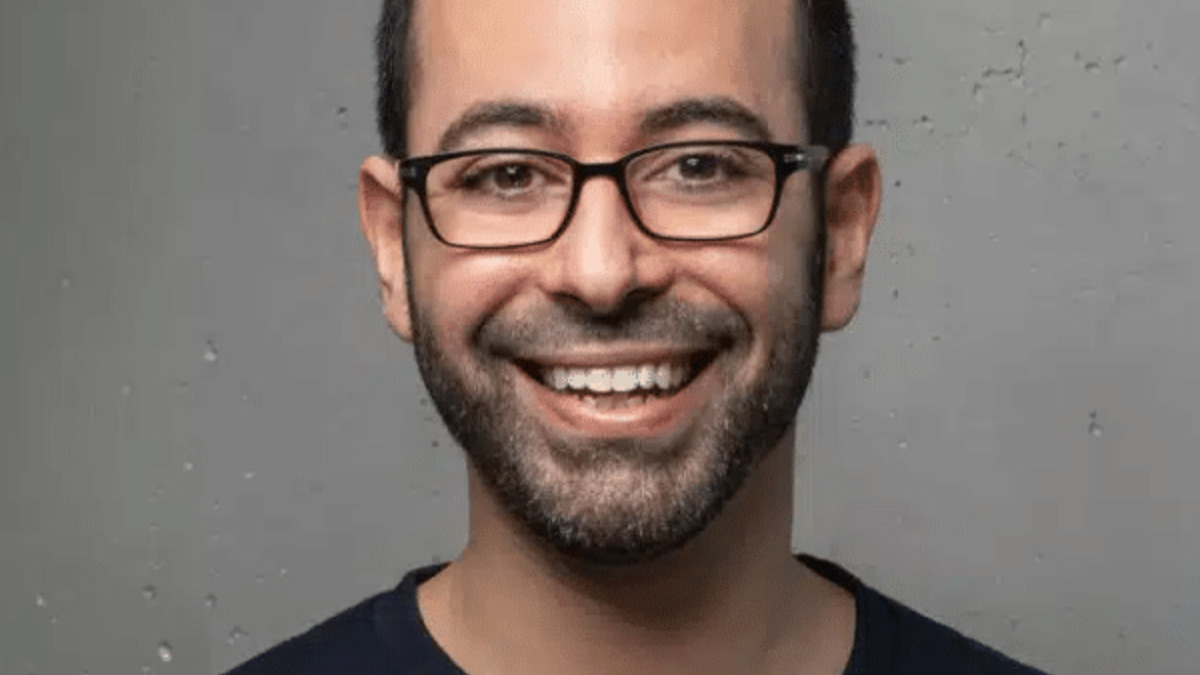 Alon Jackson co-founded Astrix Security in 2021 with Idan Gour, both veterans of Israel's Unit 8200.
Source: astrix.security
Alon Jackson co-founded Astrix Security in 2021 with Idan Gour, both veterans of Israel's Unit 8200.
Source: astrix.security
Where It Falls Short
The acquisition signals Cisco's direction, but integration takes time. The announcement blog lists Cisco Identity Intelligence, Secure Access, and Duo as integration targets - none of which are live yet with Astrix capabilities. Enterprise customers looking for coverage today are still launching Astrix as it was before the deal closed.
There's also a visibility problem that no acquisition fixes. Astrix knows about the agents you've registered with the platform. Shadow AI - the model an engineer launched via a personal API key to a personal cloud account - stays invisible until you've connected the platform to every corner of your environment. Most enterprises haven't done that mapping even for human identities.
Pricing post-acquisition is unclear. For organizations already running Cisco's security stack, Astrix may fold in without a new procurement cycle. For teams not already on Cisco, adding a vendor relationship to get agent identity management adds friction at exactly the moment adoption is accelerating.
And while Cisco is betting on NHI as a growth category, the market is moving. CrowdStrike, Palo Alto Networks, and several smaller vendors have announced NHI features in the last six months. Cisco paid a premium to enter with a purpose-built platform rather than bolting on features - but the competitive moat depends on execution speed in integrating Astrix before others catch up.
For teams already shipping agents into production, the practical question isn't whether to govern NHIs - it's which tooling layer fits your existing infrastructure. The best AI cybersecurity tools guide covers available NHI and agent security options alongside Astrix's standalone capabilities before the Cisco integration lands.
Sources:
- Securing the Agentic Workforce: Cisco Announces Intent to Acquire Astrix Security
- Cisco acquires AI security startup Astrix for $400 million
- Securing AI Agents: Interview with CEO Alon Jackson
- Cisco Reimagines Security for the Agentic Workforce
- Cisco just made two moves to own the AI infrastructure stack
